Emails can be sent through Office365 email servers using either:
- Authenticated Client SMTP, or
- SMTP Relay (using an Outlook connector)
Authenticated Client SMTP is the preferred option. SMTP Relay may be deprecated by Microsoft
Authenticated SMTP
Authenticated SMTP requires authentication to be enabled at the Microsoft 365 Tenant and the Mailbox level. It is now enabled by default.
The per-mailbox setting to enable (or disable) SMTP AUTH is available in the Microsoft 365 admin centre or Exchange Online PowerShell.
- Open the Microsoft 365 admin center and go to Users > Active users.
- Select the user, and in the flyout that appears, click Mail.
- In the Email apps section, click Manage email apps.
- Verify the Authenticated SMTP setting: unchecked = disabled, checked = enabled.
- When you’re finished, click Save changes.
In SPM/PHM configure the options in Setup > Provider > Email (for each Provider)
SMTP Server Settings
SMTP Server Name: smtp.office365.com (or outlook.office365.com)
SMTP Encryption: TLS
SMTP Server Port: 587 (needs to be an open Outgoing port)
Account Authentication
SMTP Authentication required
Authentication Method: AUTO or LOGIN
Account Username: The email address of a user account
Account Password: The password for the user account
Note:
Enable SMTP AUTH for specific mailboxes
The per-mailbox setting to enable (or disable) SMTP AUTH is available in the Microsoft 365 admin center or Exchange Online PowerShell.
- Open the Microsoft 365 admin centerand go to Users > Active users.
- Select the user, and in the flyout that appears, click Mail.
- In the Email appssection, click Manage email apps.
- Verify the Authenticated SMTPsetting: unchecked = disabled, checked = enabled.
- When you’re finished, click Save changes.
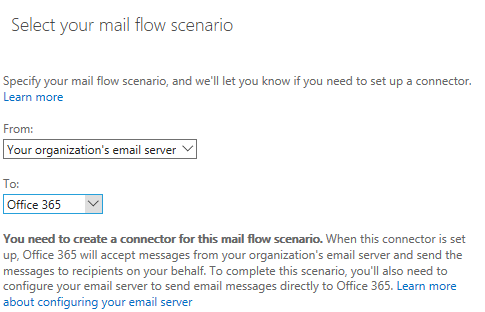
SMTP Relay
In SPM/PHM (release 409.6 or newer) configure the options in Setup > Provider > Email (for each Provider)
SMTP Server Settings
SMTP Server Name: <your-domain>.mail.protection.outlook.com
SMTP Encryption: TLS
SMTP Server Port: 25 (needs to be an open Outgoing port)
Account Authentication
SMTP Authentication NOT required
Troubleshooting
- Use the Check Connection and Send Test Email.
Look at the log as it will explain the problem. Scroll to the bottom of the log for the most recent entry. - Check port 25 or 587 are open (Use Telnet if you are not sure)
- Check .NET Framework 4.8 or newer is installed.
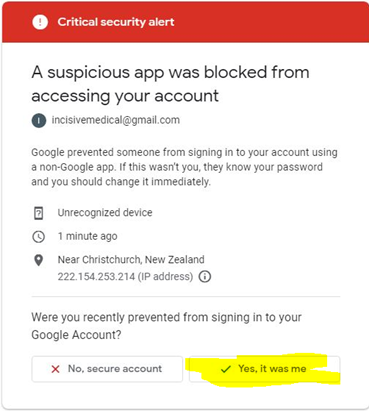
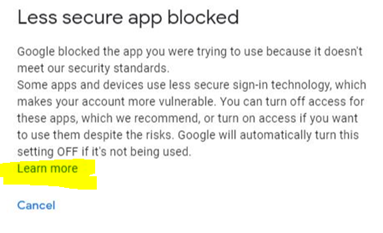
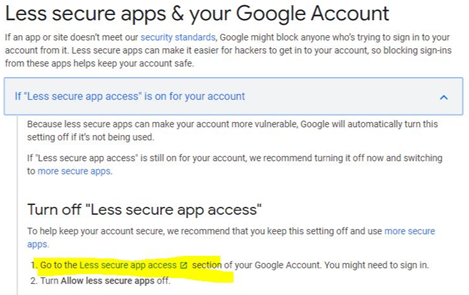
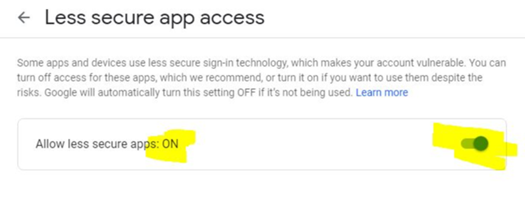
- Get your Office365 administrator to go to the Azure Active Directory and check the Sign-In logs to view the connection attempts.